How to Hack a Sequoia Touch-Screen Voting Machine
UC Computer Scientists Release Video on How to Hack a Sequoia Touch-Screen Voting Machine
-- Brad Friedman bradblog.com
Experts from CA's 'Top-to-Bottom Review' of E-Voting Systems Demonstrate How to Insert Virus, Access Machines Without Disturbing 'Security Seals' in Hack Which Would Not Be Discovered Even in 100% Audit of 'Paper Trails'
Single Malicious Individual Shown Flipping Entire 'Touch-Screen w/ Paper-Trail' Election in Seconds...
The Computer
Security Group at the University of California Santa Barbara
(UCSB) has released a short, chilling video
demonstrating how a single person can hack an election on a
touch-screen voting system --- even one with a so-called
"Voter Verifiable Paper Trail" (VVPAT) added to it --- in
such a way that it is highly unlikely that the manipulation
would ever be detected by either the public or election
officials.
The video which shows "just examples of the different ways in which the system can be compromised" is the latest in a similar string of such demonstrations that have been released over the last two years, all showing how easily electronic voting systems can be tampered with, often undetectably.
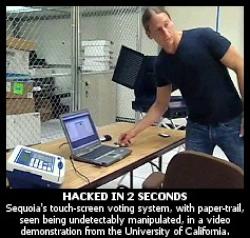
In the UCSB video posted below, the hack of Sequoia voting system being prepared for use in an entire county, is done in approximately 3 seconds, by a single person with simple insider access and a $10 USB thumb drive. Every machine used in the county, in such a case, would be effected. Moreover, the viral hack would not be discovered by pre-election "Logic and Accuracy" testing --- in cases were election officials actually bother to perform such tests prior to elections --- nor would it likely be discovered even in the event of a complete, 100% post-election audit of the touch-screen "paper-trail" records.
The hack demonstration, prepared by the UCSB scientists as part of California's 2007 "Top-to-Bottom Review" of all of the state's e-voting systems, also reveals how so-called "security seals" placed on such machines after they've been programmed for an election, can be easily defeated without detection...
How and Why It Was Done...
The landmark California study, which employed dozens of the world's top computer scientists and security experts, was commissioned by Sec. of State Debra Bowen. The first-of-its-kind, independent state analysis, included hack tests --- so-called, "Red Team" attacks --- to analyze the security of the e-voting systems. All of the systems studied were easily defeated by the testers.
The UCSB group was in charge of the analysis of voting machines made by Sequoia Voting Systems.
The methods used in the hack of a Sequoia Edge direct recording electronic (DRE, touch-screen) system --- a system which includes the Sequoia Verivote paper-trail printer, as seen in the video --- were original described in the Red Team security analysis [PDF] of the Sequoia systems as published by the Secretary of State.
The video demonstrating the voting system manipulation was prepared at the same time, but had not been released publicly until now, despite the UCSB Security Group having encouraged the Secretary of State's office to do so for some time. The scientists involved in the tests declined to speak on the record as to their reasons for releasing it on their own at this time.
"We found a number of major flaws that can be exploited to compromise the integrity, confidentiality, and availability of the voting process," explains the UCSB website where the video was released. "In particular, we developed a virus-like software that can spread across the voting system, modifying the firmware of the voting machines."
The page goes on to explain that "The modified firmware is able to steal votes even in the presence of a Voter-Verified Paper Audit Trail (VVPAT)."
In addition to the hack of the paper-trail touch-screen system, the UCSB scientists also demonstrate, in the video, how the Sequoia Edge touch-screen voting system may be accessed and manipulated even after so-called "security seals" have been applied to the machine following pre-election programming. The members of the team in the demonstration are seen access the system, while the plastic "security seals" are remain undisturbed in the process.
"Security seals" of this type, as used in California and elsewhere --- seen being easily defeated in the video --- have been cited by election officials and voting machine companies alike as key to the secure use of electronic voting machines such as the one seen being hacked in the video above.
E-Voting "Fatally Flawed"...
"The video shows how one can use a simple USB key to infect the laptop used to prepare the cards that initialize the various voting devices. As a result, the cards are loaded with a malicious software component," UCSB explains.
"When a card is inserted in a voting terminal, the malicious software exploits a vulnerability in the terminal loading procedure and installs a modified firmware, effectively 'brainwashing' the terminal. Later, when the terminal is used by the voters to cast their votes, the firmware uses a number of different techniques to modify the contents of the ballots being cast"
The UCSB Security Group page notes that electronic voting systems are exceedingly vulnerable to malicious manipulation of the type demonstrated in their video.
"While most critical systems are continuously scrutinized and evaluated for safety and correctness, electronic voting systems are not subject to the same level of scrutiny," they write.
"A number of recent studies have shown that most (if not all) of the electronic voting systems being used today are fatally flawed, and that their quality does not match the importance of the task that they are supposed to carry out."
The Latest of Many Such E-Vote Hack Demonstrations...
The Sequoia Edge system seen being hacked in the video above is the same type of system on which The BRAD BLOG had revealed another serious flaw, just days before the 2006 general election. As we reported at the time, a yellow button on the back of each voting machine (as can be seen in the UCSB video as well) can be pressed in such a way as to put the system into "manual mode," allowing for an unlimited number of votes to be cast by a single individual.
The hack demonstration video published by the California academics wouldn't be the first such video to detail exactly how an electronic voting system can be hacked by a single malicious individual. Other notable cases include:
- A 2006 Princeton University study revealed how to carry out a similar viral attack on a Diebold touch-screen voting systems, resulting in the spread of a vote-flipping virus, that would spread from machine to machine after access to just one of them (DISCLOSURE: The machine used in Princeton's testing was supplied to us by a Diebold insider. We then passed it on to the university for the first such independent study of such a voting system.) Story here, video demo here...
- While the Princeton scientists also demonstrated how the lock on a Diebold touch-screen system could be opened with either a standard hotel mini-bar key --- or even a paper clip in about 10 seconds time --- another enterprising individual found he was able to fashion a homemade key that would open the Diebold system as well. The key was made after modeling it after a photograph of the key --- the same one is used for every Diebold machine --- as, incredibly enough, posted on the company's website. Story here, video here...
- A 2006 HBO documentary, Hacking Democracy, showed a paper-based, Diebold optical-scan tabulator being manipulated in a mock election which flipped the results reported by the system. That landmark hack disclosed still-uncorrected security flaws in all Diebold systems (both touch-screen and optical-scan). The exact same Diebold, paper-based tabulators were used in last January's anomalous New Hampshire primary. Video here...
- A one-minute 2006 hack demonstration of an e-voting system used in the Netherlands, shows how a key chip can be replaced in such a system in just 60-seconds. PDF analysis here, video here...
"Paper-Trails" Are Meaningless...
The UCSB demonstration of the Sequoia Edge with Verivote hack is notable, however, given that many proponents of electronic voting --- including many Democrats and their various public interest group supporters, such as People for the American Way (PFAW), Common Cause, Verified Voting, NYU's Brennan Center for Justice and others --- have argued that adding paper-trails (VVPATs) to such systems would mean that any manipulation of the system would be discovered during an examination of the paper-trails after an election. As the video shows, post-election examinations or audits of touch-screen paper-trail systems hacked in this way, would not easily --- if at all --- reveal the manipulation.
Following Bowen's "Top-to-Bottom Review", touch-screen systems made by Sequoia, Diebold and ES&S were restricted to use of one-per-precinct only, in order to marginally meet the disabled-accessible voting requirements of the federal Help America Vote Act (HAVA). She also required a 100% hand-count of the paper-trails produced by such systems, even though the UCSB team found that such audits would not necessarily catch voting system manipulation. Many states around the country continue to allow unfettered use of such hackable voting systems. None, other than California, require 100% post-election audits.
A similar DRE system made by Hart InterCivic was allowed for full use, almost inexplicably, after the California testing, in two different counties.
Despite the quickly mounting scientific evidence persuading against the use of such systems in American elections, Congressman Rush Holt (D-NJ) and Senator Diane Feinstein (D-CA) have proposed a number of bills which would allow for the continued use of touch-screen voting systems with paper-trails. The Republican caucuses in each chamber have so far stymied all such legislation, even as they argue in favor of the use of all such electronic systems, with or without the often misleading paper-trails.
MORE COVERAGE: See John Byrne at RAW STORY and Rady Ananda at OpEdNews.


 Richard S. Ehrlich: Strait Of Hormuz Blockades & Thailand's Land Bridge
Richard S. Ehrlich: Strait Of Hormuz Blockades & Thailand's Land Bridge Keith Rankin: 'I Am A Semite'
Keith Rankin: 'I Am A Semite' Binoy Kampmark: Show Me The Money - A Loutish Administration Confronts A Craven Congress
Binoy Kampmark: Show Me The Money - A Loutish Administration Confronts A Craven Congress Ian Powell: Do Wellington Floods, Climate Change And Wealth Accumulation Equal “Suicidal Capitalism”?
Ian Powell: Do Wellington Floods, Climate Change And Wealth Accumulation Equal “Suicidal Capitalism”? Ramzy Baroud: The Pendulum Swings - The Slow Death Of Europe’s Pro-Israel Consensus
Ramzy Baroud: The Pendulum Swings - The Slow Death Of Europe’s Pro-Israel Consensus Dr Nasim: Poem From Gaza - Her Smile
Dr Nasim: Poem From Gaza - Her Smile